Security is always an important topic in any field. Web application security is not a different matter. In 2019, web application security becomes so important that common people who use internet as a daily basis should have at least some basic knowledge about it.
In this post, I will discuss the facts that makes web application security as an important and vital topic of interest in 2019. After completely reading this post, you will be able to know why you would care for it in 2019, what are the different impacts of it and finally what are the most common threats to web application security.

Web application security is a separate department of information security that deals specifically with web application's vulnerabilities.
Why do I care about Web Application Security?

Financial Loss
The average cost of a hack is $3,000,000, not all types of attacks will be around that figure. Some attacks are more costly than others. Costs also differ with the frequency of an attack against an organization.
The following screenshot is Accenture's graphical representation of the costs of the most common attacks based on their frequency in 2016 and 2017. This data was collected from 254 companies around the world:
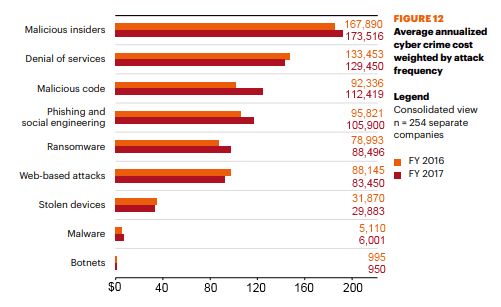
To interpret this data, one should note that frequency was taken into consideration. Consequently, the most frequent attacks had higher averages. As can be seen from the graph, insider threats are the most frequent and costly threats to an organization.
Attacks related to malicious insiders led to losses averaging $173,516 in 2017. The reason for this high cost is due to the amount of information that insider threats possess when carrying out an attack.
Loss Of Service
Denial-of-service (DoS) attack is a type of cyber attack where a malicious user targets a server or other device so that it is unavailable to its intended users by interrupting server's normal functioning.
A server or device can handle a certain limit of requests. What this attack does is, it floods the server by sending requests until the server or device is unable to process new incoming requests. A DoS attack is done by using a single computer to launch the attack.
Distributed Denial-of-service (DDoS) is the most devastating form of DoS that uses multiple infected systems as source of attack. Those systems can include computers and other networked resources.
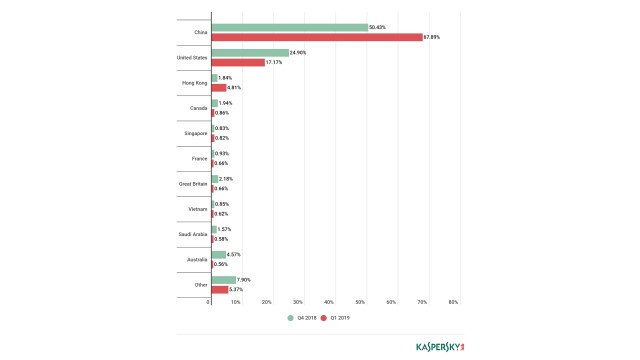
Following screenshot depicts DDoS attacks country-wise for the year 2018 and 2019.
Identity Theft
This type of attack is done by obtaining personally identifiable information, like driver's license number, Social Security number etc. in order to impersonate someone else.
Phishing and spam emails are used as methods of tricking people to collect information from them. The email may contain attachments with malware that is programmed to steal personal data or sending links to fraudulent websites that has the same look and feel like authentic websites where the person would be prompted to enter their information.
Website Infection
This type of attack is triggered by creating a malicious website that attempts to install malware (a software designed to disrupt your system, gather your personal information, or in a worst-case scenario gain total access to your system) onto your device.
The malicious website might ask for permission to install one program, but install a completely different one.
What are Common Threats to Web Application Security?
According to OWASP(The Open Web Application Security Project) following are the most critical web application risks.
- Injection
- Broken Authentication
- Sensitive Data Exposure
- XML External Entities
- Broken Access Control
- Security Misconfiguration
- Cross-Site Scripting
- Insecure Deserialization
- Using Components with Known Vulnerabilities
- Insufficient Logging & Monitoring
Final Words
So, I discussed the facts to consider about web application security in 2019. I hope you find our article helpful to you. If you find this post as helpful, don't forget to share it with others. Thank you!